It's a great example of task which looks simple but escalates to enormous complexity.
My task was very simple: create Google Storage Bucket (Same as Amazon AWS S3) and create specific user which can upload data to it without using global system account. I needed access_key and secret_key which are compatible with s3cmd and Amazon S3.
My plan was to use this key for CI/CD system and reduce potential consequence from leaking this key.
First of all, we need to enable IAM API open link and then click "Enable the IAM API".
Then we need to create so called "Service account" which will belong to our CI/CD system. To do it open same link and scroll to "Creating a service account".
In my case link was this but it may change with time.
Then you need to specify project where you keep your bucket.
Then click "Create service account" on the bottom of page. Fill only name and do not allocate any permisisons for it. It will create service account for you in format: xxxx@project-name.iam.gserviceaccount.com
Then go to Cloud Storage section in your management console link
Select your bucket, go to permissions, click "Grant Access" and in section Principals insert "xxxx@project-name.iam.gserviceaccount.com" then for Assign Roles select "Cloud Storage" on the left side and select "Storage object Admin" on right side then click Save.
We're not done. We need to create access_key and secret_key for this user.
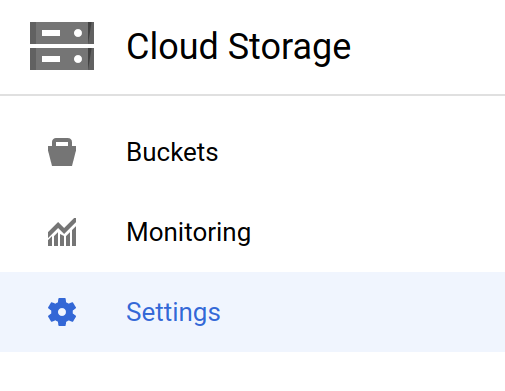
To do it open "Cloud Storage" section in console.
On the left side click "Settings". Then on the right side click Interoperability.
Then follow to "Access keys for service accounts" and click "Create a key for another service account". In this list select our service account created previously and click create key.
Then copy both keys as they will disappear immediately after.
Then provide both keys as AWS_ACCESS_KEY_ID and AWS_SECRET_ACCESS_KEY as environment variables for s3cmd.




No comments :
Post a Comment
Note: only a member of this blog may post a comment.